ASEC Weekly Phishing Email Threat Trends (April 9th, 2023 – April 15th, 2023)
AhnLab Security Emergency response Center (ASEC) monitors phishing email threats with the ASEC automatic sample analysis system (RAPIT) and honeypot. This post will cover the cases of distribution of phishing emails during the week from April 9th, 2023 to April 15th, 2023 and provide statistical information on each type. Generally, phishing is cited as an attack that leaks users’ login account credentials by disguising as or impersonating an institute, company, or individual through social engineering methods. On a broader note, the act is a technical subterfuge that enables the threat actor to perform attacks such as information leaks, malware distribution, and fraud against various targets. The focus of this post will be on the fact that phishing attacks mainly occur through emails. We will also provide a detailed classification of various attack methods that are based on phishing emails. Furthermore, we will make an effort to minimize user damage by introducing new attack types that have never been found before and emails that require users’ caution, along with their keywords. The phishing emails covered in this post will only be those that have attachments. Emails that have malicious links in the body without attachments will be excluded.
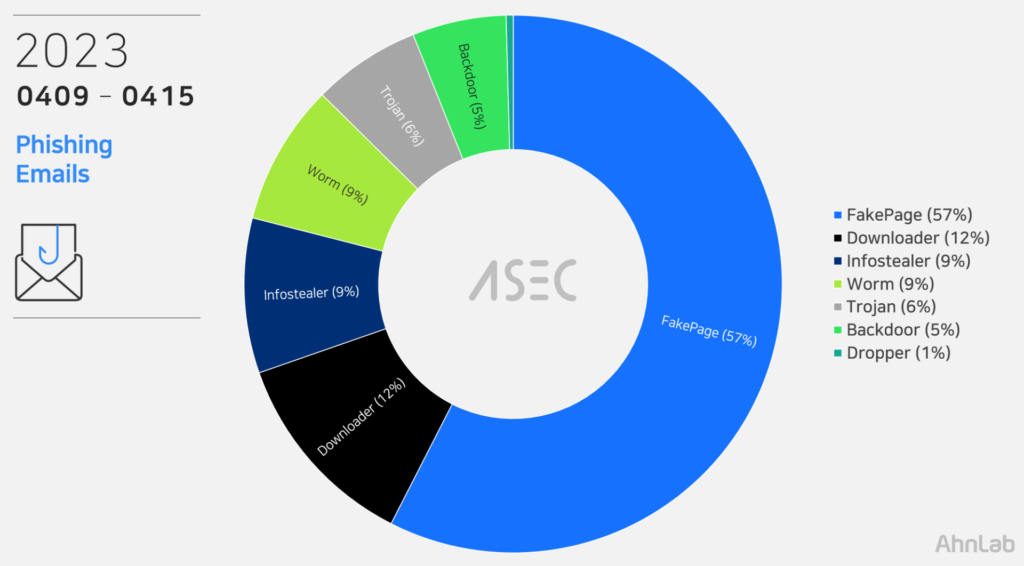
Phishing Emails
During this week, the most prevalent threat type seen in phishing email attachments was FakePage with 57%. FakePages are web pages where the threat actor has imitated the screen layout, logo, and font of the real login pages or advertising pages, leading users to enter their account and password information. The input information is sent to the threat actor’s C2 server or used to induce users to access other fake websites. See <FakePage C2> below The second most prevalent threat type was Downloader (12%), which includes loaders such as SmokeLoader and GuLoader. It was then followed by Worm (9%) and Infostealers (9%) like AgentTesla and FormBook that leak user credentials saved in web browsers, emails, and FTP clients. Aside from those mentioned above, Trojan (6%), Backdoor (5%), and Dropper (1%) types were detected. The threat types using phishing email attachments and their order of prevalence are similar to the order of malware distribution published weekly in the <ASEC Weekly Malware Statistics>.
File Extensions in Phishing Emails
We have identified which file extensions were used by the threats above for the distribution of email attachments. FakePages were distributed through web pages script (HTM, HTML, SHTML) documents that must be executed with a web browser. Other malware, including Infostealer and downloader, came attached to emails with file extensions including compressed files (RAR, ZIP, 7Z, GZ, etc.).
Cases of Distribution
The following are distribution cases that occurred during the week from April 9th, 2023 to April 15th, 2023. The cases will be classified into FakePage and malware types, including Infostealer, Downloader, Exploit, and Backdoor. The numbers in email subjects and attachment filenames are unique IDs and may vary depending on the email recipient. Distribution cases with Korean subjects were also found. These are cases that specifically targeted Korean users instead of propagating themselves globally using identical English subject and texts.
Case: FakePage
Email Subject
Attachment
DHL ARRIVAL (CONTAINER) Seaport Import Customs Information Submission Form – Proforma Invoice, Packing List & BL Copy
invoice & Tracking NumberHT2.html
FedEx Shipment Arrival Notice
AWB#989345874598.html
[FedEx] Tariffs payment notice (Tax Invoice)
Tax_Notification.html
PO912048302417 Payment Copy
PI0437834 Payment Confirmation.html
DHL Express Shipment Confirmation
CustomInvoice_8278124481.pdf.htm
Fw: Deliver BL / INV / PL
Shipping Document (1).html
FedEx Shipping Document / Invoice Receipt
INVOICE_AWB.htm
Incoming Shipment Invoice
AWB#03773N .htm
Updated quotation
qoutation order879999.shtml
Cigna HealthCare ACH Settlement: Please review and Sign
Healthcare-Claim-Notification.pdf
Shipment Booking Confirmation – BL Draft is Ready for Review – Original Scan copies of Document
Draft Bill of Lading__Shipping Document.htm
Overdue Balance Notice : TT_COPY_FOR_VNQ5160KTR-E_3000PCS
AWWDPAYMENT DETAILS.html
New DHL Shipment Document Arrival Notice / Shipping Documents / Original BL, Invoice & Packing List
(DHL) Original BL, PL, CI Copies.htm
FW: REVISED PO’S
SOA for 2023.shtml
DHL Shipping Document / Invoice Receipt
DHLShippingdocs.htm
EFT/ERA Cigna HealthCare ACH Payment: Completed_ Please Review and Sign
ACH-Deposit-Completed.pdf
PO#13012022N_ 新命令
PO#13012022N.html
*** NOTIFICATION FOR INCOMING DHL SHIPMENT ***
DHL Express Notification.XLS.html
TRACK: EXPRESS (Shipment Notification)
DHL EXPRESS shipping docs.shtml
(Invoice) Original BL, PL, CI_AWB#71******90
****@**********.com DHL Express Notification.PDF.html
PO#28124758
28124758.htm
Shipment Notification (TRACK EXPRESS)
Track_ Express Shipping Docs.shtml
Statement of Account (SOA) Paid
Payment_Copy.PDF.html
DHL Express
DHLSHIPPINGDOCS.htm
Fwd: Past due balance SWIFT copy.
invoice_proforma2.html
SF Express: eNotification sent
eimDoc.html
INV Remittances 2nd request 711647666′
INV-PAY0080388388.html
QUOTATION FOR MAY SHIPMENT
QUOTATIONS.pdf
FW: Payment 12 Apr 2023
Wire Transfer confirmation.shtml
FYI SWIFT COPY FEDSD34455532536737DWES
FEDSD34455532536737DWES.html
Your parcel has arrived urgent pick up needed today.
AWB #8347630147.htm
Case: Malware (Infostealer, Downloader, etc.)
Email Subject
Attachment
Related to 2023 Korea-U.S. Policy Forum
[Attachment] Profile Template.doc
Reply: Reply: [DHL] Acceptance of Import Declaration (Payment Before Acceptance) – 1000452436
Import declaration acceptance statement-1000452436.rar
Fwd: Quotation Invitation
Quotation Invitation 000111.pdf.GZ
Re: Adtours travel, inc
Booking_8986007pdf (1).7z
RE: BOOKING
Booking_8986007pdf.7z
Fwd: SNE-20210123
SNE-20210123.rar
RFQ Bidding of 38D OBA project
RFQ Bidding of 38D OBA project.rar
FW: SWIFT Transfer REG:NO: SWFT7900896875
SWFT7900896875.7Z
Our new order# F.94_100023010
DOc 000399288299991.rar
PAYMENT REMINDER
PAYMENT REMINDERPDF.GZ
SOA
SOA.r01
PTC-04-0-03643 / KMTCSHAK477267
CZ3C126-2409.xls
NEW REQUIREMENT 10.04.2023
REQUIREMENT100420230001001010.pdf.gz
Advice & SWIFT copy: CustID 52579XXXX_6031NMDC0002724_FORESTAL MIMOSA LIMITED
CustID 52579XXXX_6031NMDC0002724.PDF.zip
QUOTATION FOR MAY SHIPMENT
ORDER SPEC_pdf.7z
RE: [Inquiry]
Quote_3500001299.r09
AW: PO-000001306
PO-000001306.r09
AW: SRY-510-9310
SRY51093IO.IMG
Re: Bokings
Confirm!.rar
SUBJECT:Advice from Standard Chartered Bank
FTT 325272022023.img.tar
DHL Shipment Notification: AWB811470484778
#AWB811470484778.rar
RE; Final Warning – Over Due Payment – Urgent Reminder!Final Warning – Over Due Payment – Urgent R….
OUTSTANDING PAYMENT.IMG
ATTENTION
AMED.IMG
ARH2301433-MODERN SPARES AND EQUIPMENT 12.04.2023
ARH PO # 2301433.pdf.7z
CV Lic. H&S Oli***ti *****
curriculum vitae Lic. H&S Oli***ti *****.zip
FW: Autogenerated mail – Vendor Payment Advice
Payment_110280.JPEG.7z
REQUISITE ORDEN NUMBER: 8499009
REQUIREMENT ORDER NO8499009.pdf.gz
RE: dubai shipments
Order_confirmation#982783.zip
[Adres dogrulanamadi (SPF:softfail)] SEHVEN YATAN TUTAR IADESI
IADESI.001
Mart-2023 Ekstreniz
Ekstrenz.gz
swift mesaji hk
SWIFT.UUE
11.04.2023 sevkiyat
SWIFT.001
Fw: About The Payment
20230412123719_TRF_MT 103.gz
NEW ORDER
PO-5418911023 and PO-5418911025.gz
sexy pictures very important
superscene.gif.scr
super sexy pictures don’t show
sex_img.gif.scr
Re: super beautiful pics private
best__pctrs.jpg.pif
sexy pics
coolact.pif
Re[5]: nice pictures
fuck-plp.gif.scr
Re[3]: very nice photos just for you
great-imgs.pif
Re[5]: very wonderful picture only for you
prvimg.jpg.pif
Re[5]: smart photos
bestpic.jpg.scr
Re[4]: very beautiful images don’t show
great-imgs.gif.pif
Re[2]: very sexy images
wild__pctrs.exe
super beautiful photo
private-phot.gif.pif
super sexy pictures
cool_pic.exe
beautiful photo very important
superimages.gif.pif
super sexy pics
cool_pic.pif
Re: very wonderful picture imortant
fuckscene.jpg.pif
wonderful pics
theimages.gif.exe
Re[5]: smart pictures
prvscene.pif
beautiful pictures
superpctrs.jpg.exe
Re: very cool pictures private
best-phot.scr
Re: super cool photos PRIVATE
best__phot.scr
very nice photos only for you
cool__pctrs.gif.exe
The ASEC analysis team has selected keywords that users must look out for, based on the distribution cases above. If these keywords are included in the subject of the email, or if the same characteristics are found, users must exercise strict caution as they may be phishing emails from threat actors.
Keywords to Beware of: ‘Import Customs’
The keyword for this week is ‘Import Customs.’ Last week, the author of the phishing email distributed the mail with the subject, “DHL ARRIVAL (CONTAINER) Seaport Import Customs Information Submission Form – Proforma Invoice, Packing List & BL Copy.” The sender impersonated the DHL shipping company, and the attachment was a phishing HTML file that started with the words ‘Invoice & Tracking,’ unrelated to the subject of the email. Upon clicking the file, a page pretending to be from the DHL shipping company is opened, and it requires the user to enter their ID and password to lookup their customs information. As such, users are advised to take closer looks at the file names of email attachments before opening them and also check if the attachments are related to the subject of the email.
Phishing URL: hxxps[:]//formcarry[.]com/s/HGNnWjQ9O0
FakePage C2 URL
When users enter their IDs and passwords on the login pages among the FakePages created by the threat actor, their information is sent to the attacker’s server. The list below shows the threat actor’s C2 addresses of fake login pages distributed during the week.
https[:]//formspree[.]io/f/myyazkbv
https[:]//vigilant-rubin[.]185-236-228-67[.]plesk[.]page/jh/Adhl[.]php
http[:]//ingitek[.]ru/bitrix/admin/csss/tt/xlss[.]php
http[:]//usxcheap[.]us/GS9/access1[.]php
https[:]//submit-form[.]com/riYXPwjH
https[:]//realmebel[.]pro/dh/dlh[.]php
http[:]//ingitek[.]ru/bitrix/admin/csss/tt/xlss[.]php
https[:]//formspree[.]io/f/myyazkbv
https[:]//submit-form[.]com/qt7uUYP3
https[:]//submit-form[.]com/IsP9wxLh
https[:]//ecstatic-chandrasekhar[.]185-236-228-67[.]plesk[.]page/chkky/Adhl[.]php
https[:]//www[.]mkcrop-kr[.]com/si/fdpxoGur23f[.]php
https[:]//submit-form[.]com/MC3ozIXM
https[:]//ecstatic-chandrasekhar[.]185-236-228-67[.]plesk[.]page/chkky/Adhl[.]php
https[:]//submit-form[.]com/kVlBCzwE
https[:]//formspree[.]io/f/myyazkbv
https[:]//www[.]btdpipe1ine[.]com/ke/fdpxoGur23f[.]php
https[:]//cranecenter[.]ru/X/processor1[.]php
https[:]//app[.]headlessforms[.]cloud/api/v1/form-submission/nQwc1kUGvU
https[:]//formcarry[.]com/s/HGNnWjQ9O0
https[:]//test[.]novostroi21[.]ru/killer/xlss[.]php
https[:]//www[.]nsggroup[.]it/,/tw/postdhll[.]php
Attacks using phishing emails are disguised with content that can easily deceive users, such as invoices and tax payments, to induce users to access fake login pages or execute malware. Fake login pages are evolving by the second to closely resemble the original pages. The attackers pack malware in compressed file formats to escape the attachment scans of users’ security products. Users must practice strict caution and refer to recent cases of distribution to avoid being exposed to infection by malicious phishing emails. The ASEC analysis team recommends users follow the email security guidelines below.
Do not execute links and attachments in emails from unverified senders until they are proven to be credible.
Do not enter sensitive information such as login account credentials until the site is found to be reliable.
Do not execute attachments with unfamiliar file extensions until they are found to be reliable.
Use security products such as antimalware software.
According to the MITRE ATT&CK framework, phishing email attacks correspond to the following techniques.
Phishing for Information(Reconnaissance, ID: T1598[1])
Phishing(Initial Access, ID: TI1566[2])
Internal Spearphishing(Lateral Movement, ID:T1534[3])
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.
The post ASEC Weekly Phishing Email Threat Trends (April 9th, 2023 – April 15th, 2023) appeared first on ASEC BLOG.
Article Link: ASEC Weekly Phishing Email Threat Trends (April 9th, 2023 – April 15th, 2023) – ASEC BLOG
1 post – 1 participant

