ASEC Weekly Phishing Email Threat Trends (April 23rd, 2023 – April 29th, 2023)
AhnLab Security Emergency response Center (ASEC) monitors phishing email threats with the ASEC automatic sample analysis system (RAPIT) and honeypot. This post will cover the cases of distribution of phishing emails during the week from April 23rd, 2023 to April 29th, 2023 and provide statistical information on each type. Generally, phishing is cited as an attack that leaks users’ login account credentials by disguising as or impersonating an institute, company, or individual through social engineering methods. On a broader note, the act is a technical subterfuge that enables the threat actor to perform attacks such as information leaks, malware distribution, and fraud against various targets. The focus of this post will be on the fact that phishing attacks mainly occur through emails. We will also provide a detailed classification of various attack methods that are based on phishing emails. Furthermore, we will make an effort to minimize user damage by introducing new attack types that have never been found before and emails that require users’ caution, along with their keywords. The phishing emails covered in this post will only be those that have attachments. Emails that have malicious links in the body without attachments will be excluded.
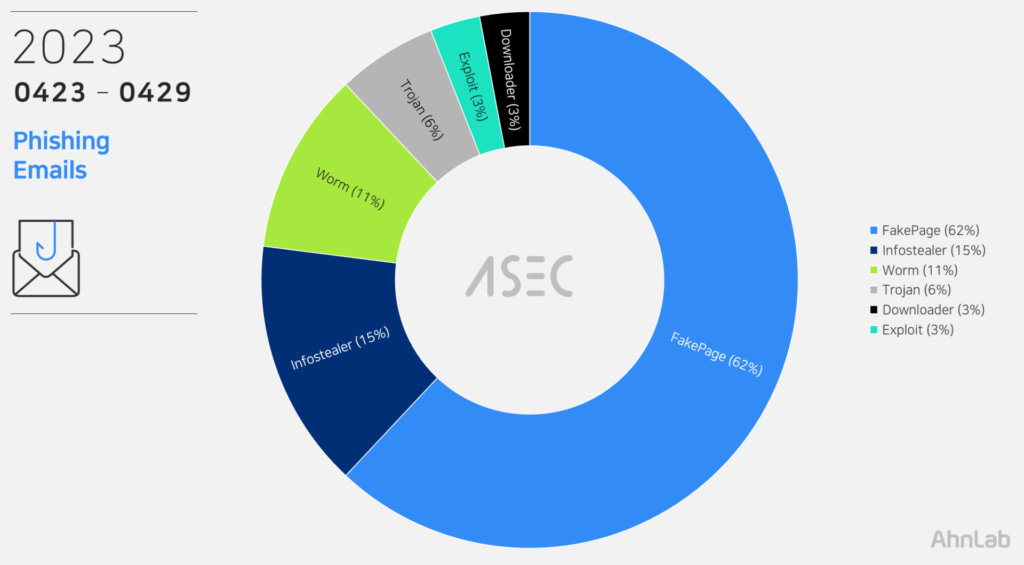
Phishing Emails
During this week, the most prevalent threat type seen in phishing email attachments was FakePage with 62%. FakePages are web pages where the threat actor has imitated the screen layout, logo, and font of the real login pages or advertising pages, leading users to enter their account and password information. The input information is sent to the threat actor’s C2 server or used to induce users to access other fake websites. See <FakePage C2> below The second in line were InfoStealers like AgentTesla and FormBook that leaks user credentials saved in web browsers, emails, and FTP clients (15%). It was then followed by Worm, which took up 11%. Worm is a type of malware that has a feature to spread, where it uses various methods for spreading, with one of them being using the SMTP protocol to send emails in mass quantity. Aside from those mentioned above, Trojan (6%), Exploit (3%), and Downloader (3%) were detected. The threat types using phishing email attachments and their order of prevalence are similar to the order of malware distribution published weekly in the <ASEC Weekly Malware Statistics>.
File Extensions in Phishing Emails
We have identified which file extensions were used by the threats above for the distribution of email attachments. FakePages were distributed through web pages script (HTM, HTML, SHTML) documents that must be executed with a web browser. Other malware, including Infostealer and downloader, came attached to emails with file extensions including compressed files (RAR, ZIP, 7Z, GZ, etc.).
Cases of Distribution
The following are distribution cases that occurred during the week from April 23rd, 2023 to April 29th, 2023. The cases will be classified into FakePage and malware types, including Infostealer, Downloader, Exploit, and Backdoor. The numbers in email subjects and attachment filenames are unique IDs and may vary depending on the email recipient. Distribution cases with Korean subjects were also found. These are cases that specifically targeted Korean users instead of propagating themselves globally using identical English subject and texts.
사례: 가짜 로그인 페이지 (FakePage)
Email Subject
Attachment
[FEDEX] Export Declaration Form Attachment – AWB – 771809695008
[FedEx] Shippingdocs.htm
Upgrade required.
******.co.kr upgrade.htm
FedEx Shipment Arrival Notice [AWB#6704537800]
FedExDocShip.html
DHL Shipment Arrival Notice [AWB#*****378004]
AWB3342DHLShipmentDocument.html
[**** Shipment] Clearance of original invoices and packing lists.
Original-invoice_******.***.htm
RE: Shipment BL/AWB # & INVOICE/PACKING LIST – 3098438290 ETD/ETA
Original Shipiing_ Doc-AWB#64492586612.pdf.html
New Purchase Order Inquiry
New Purchase Order Inquiry-08-22.htm
New Order – PO-KM19-141701
PO-KM19-141701.htm
RV: ! Urgent Purchase Order
PO603.shtml
CIPC Annual Returns-K2018772381
COR14.1A.html
Payment: ACH Payment on hold
ACH Deposit Agreement.html
[SEC=OFFICIAL:Sensitive, ACCESS=Personal Data-Privacy]
Personal Data-Privacy-SecureMessageAtt.html
Re: Overdue Outstanding Payment
Payment_Invoice.shtml
Congratulations – IMF Donation
b4334540-ea22-11ed-bb90-44a842253043.html
[FedEx] Import Tax Payment Deadline Information (INV and AWB)
FedEx_AWB Original.html
Email deactivation notification
attachment-1._
RE: Shipment BL/AWB # & INVOICE/PACKING LIST – 721499777319
Original Shipiing_ Doc-AWB#44142554808.pdf.html
DHL Arrival Notice: New DHL Shipment Document / Shipping Documents / Original BL, Invoice & Packing List
New DHL Shipment Document Arrival Notice _ Shipping Documents _ Original BL, Invoice & Packing List.shtml
RE: Shipment BL/AWB # & INVOICE/PACKING LIST – 647551940416
Original Shipiing_ Doc-AWB#67171342267.pdf.html
DHL Cargo Arrival Information [AWB#*****378004]
DHLParcelShipmentDoc.html
RFQ.
Purchase-request_pdf.shtml
Congratulations – IMF
a21197c0-ea3d-11ed-8e27-44a842253043.html
Congratulations – IMF Grant
37e5b7b0-ea23-11ed-910b-44a842253043.html
Greetings – IMF Grant
3aa85621-ea4f-11ed-b728-44a842253043.html
Congratulations – IMF Empowerment Grant
b68281de-ea21-11ed-9b25-44a842253043.html
사례: 악성코드 (Infostealer, Downloader 등)
Email Subject
Attachment
Request_for_Quote_106_-_Supply_of_Flex_Connector_for_Diesel_Engine_Exhaust
Request for Quote.rar
new project order and pricing.
Doc_2152_182239pdf.7z
Order ******
230327-1 Offer(******) -CCK-3. 2unit IR (Rev.1).gz
Booking for my Birthday
Reservation for Birthday Party.docx
CBFI CV3000 CONTRACT COPY/CARGO MANIFEST
CBFI CV3000 Contract_Copy_2Original-20230426.doc
REMITTANCE TT COPY
TT COPY.xls
FW: URGENT PURCHASE ORDER
PURCHASE ORDER.rar
RE: PRICE FOR DISCOUNT -BEMS-477
PRICE DISCOUNT QOUTATION.r00
RE: Product Inquiry and RFQ
CATALOGUE AND PRODUCTS SPECIFICATION.r00
Autogenerated mail – Payment Advice
Payment Advice 001076723030.pdf.gz
Fw: RFQ
Request for quotation – April 2023.pdf.zip
New order Request
New order.zip
New Order Purchase Inquiry
Purchase Inquiry.r00
Re: Re: Po No. 0456/ZHS/23T ORDER
KERGYK109008_ORDER.zip
Payment Copy
20230425-Mt103-80012372654390.zip
R: R: Payments
REMITTANCE COPY_20230427_912309172542311.zip
DHL AWB – Invoice & Shipping Documents
DHL AWB – Invoice & Shipping Documents.zip
Aw: About the payment
SWIFT Message_MT 103_00101881022.gz
RE: order
Quote_2200001484.r09
STOCK REQUEST for 01 x 20′ Container (10 Pallets) –
REVISED CONTRACT.zip
TRUCKING INSTRUCTIONS – EX SIN TO SYD – APR23
Export Trucking Instruction.zip
****** BANKASI A.S. 25.04.2023 ***** ********
****bank_*****_20230425_073809_405251-PDF.r27
urgent new orders packaging and delivery.
Doc_251_71190_06123pdf.7z
Re: smart picture PRIVATE
wildaction.jpg.scr
Re[3]: cool photos just for you
great-plp.pif
sexy photo
myact.jpg.pif
Re: wonderful pictures
great_imgs.jpg.exe
Re[3]: beautiful picture
prvpic.gif.pif
beautiful images imortant
coolimg.gif.pif
Re[5]: beautiful pictures very important
great_pic.jpg.exe
Re: smart photo very important
great__plp.scr
Re[2]: very nice photos
wild_phot.jpg.scr
nice photos private
privateaction.pif
very nice photo
super_act.gif.pif
Re[2]: super wonderful photos don’t show
fuck-img.gif.scr
Re[2]: very beautiful photos
best__plp.jpg.pif
cool pictures imortant
privateimgs.exe
Re[5]: super cool images just for you
wild__phot.gif.pif
super sexy photo
cool-pic.jpg.pif
Re[5]: sexy photo private
great-imgs.jpg.pif
beautiful picture
myplp.gif.scr
Re[5]: very cool photos only for you
wild_phot.scr
Re[2]: super nice photos just for you
priv-act.jpg.scr
Re[4]: very wonderful picture
great__photos.gif.scr
Re[3]: wonderful photos just for you
fuck_img.pif
The ASEC analysis team has selected keywords that users must look out for, based on the distribution cases above. If these keywords are included in the subject of the email, or if the same characteristics are found, users must exercise strict caution as they may be phishing emails from threat actors.
Keywords to Beware of: ‘Disguised Image File’
The keyword for this week is ‘Disguised Image File.’ The Worm-type malware disguised as image files (coolimg.gif.pif) has been found among phishing email types. Threat actors arouse the curiosity of users through eye-catching messages to entice users into executing the malware disguised as an image file. As shown below, the file was distributed with the extension pif. This is an executable file just like the EXE extension. As such, users are advised to take closer looks at the file names of email attachments before opening them and also check if the attachments are related to the subject of the email.
FakePage C2 URL
When users enter their IDs and passwords on the login pages among the FakePages created by the threat actor, their information is sent to the attacker’s server. The list below shows the threat actor’s C2 addresses of fake login pages distributed during the week.
https[:]//formspree[.]io/f/myyazkbv
https[:]//formspree[.]io/f/xayznrae
https[:]//press[.]genesis[.]ru/zeta/xlss[.]php
https[:]//www[.]coupedusud[.]fr/upload/accueil/speed/next[.]php
https[:]//drmaysilveira[.]com[.]br/wp-content/onyi/excelz/index[.]php
https[:]//anmelden[.]ml/[.]well-known/ac/pdf[.]php
https[:]//steelfirst[.]com[.]au/new/1drv[.]php
https[:]//tinyurl[.]com/bdfavnm7
https[:]//press[.]genesis[.]ru/ziv/xlss[.]php
Attacks using phishing emails are disguised with content that can easily deceive users, such as invoices and tax payments, to induce users to access fake login pages or execute malware. Fake login pages are evolving by the second to closely resemble the original pages. The attackers pack malware in compressed file formats to escape the attachment scans of users’ security products. Users must practice strict caution and refer to recent cases of distribution to avoid being exposed to infection by malicious phishing emails. The ASEC analysis team recommends users follow the email security guidelines below.
Do not execute links and attachments in emails from unverified senders until they are proven to be credible.
Do not enter sensitive information such as login account credentials until the site is found to be reliable.
Do not execute attachments with unfamiliar file extensions until they are found to be reliable.
Use security products such as antimalware software.
According to the MITRE ATT&CK framework, phishing email attacks correspond to the following techniques.
Phishing for Information(Reconnaissance, ID: T1598[1])
Phishing(Initial Access, ID: TI1566[2])
Internal Spearphishing(Lateral Movement, ID:T1534[3])
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.
The post ASEC Weekly Phishing Email Threat Trends (April 23rd, 2023 – April 29th, 2023) appeared first on ASEC BLOG.
Article Link: https://asec.ahnlab.com/en/52375/
1 post – 1 participant


