ASEC Weekly Phishing Email Threat Trends (May 7th, 2023 – May 13th, 2023)
AhnLab Security Emergency response Center (ASEC) monitors phishing email threats with the ASEC automatic sample analysis system (RAPIT) and honeypot. This post will cover the cases of distribution of phishing emails during the week from May 7th, 2023 to May 13th, 2023 and provide statistical information on each type. Generally, phishing is cited as an attack that leaks users’ login account credentials by disguising as or impersonating an institute, company, or individual through social engineering methods. On a broader note, the act is a technical subterfuge that enables the threat actor to perform attacks such as information leaks, malware distribution, and fraud against various targets. The focus of this post will be on the fact that phishing attacks mainly occur through emails. We will also provide a detailed classification of various attack methods that are based on phishing emails. Furthermore, we will make an effort to minimize user damage by introducing new attack types that have never been found before and emails that require users’ caution, along with their keywords. The phishing emails covered in this post will only be those that have attachments. Emails that have malicious links in the body without attachments will be excluded.
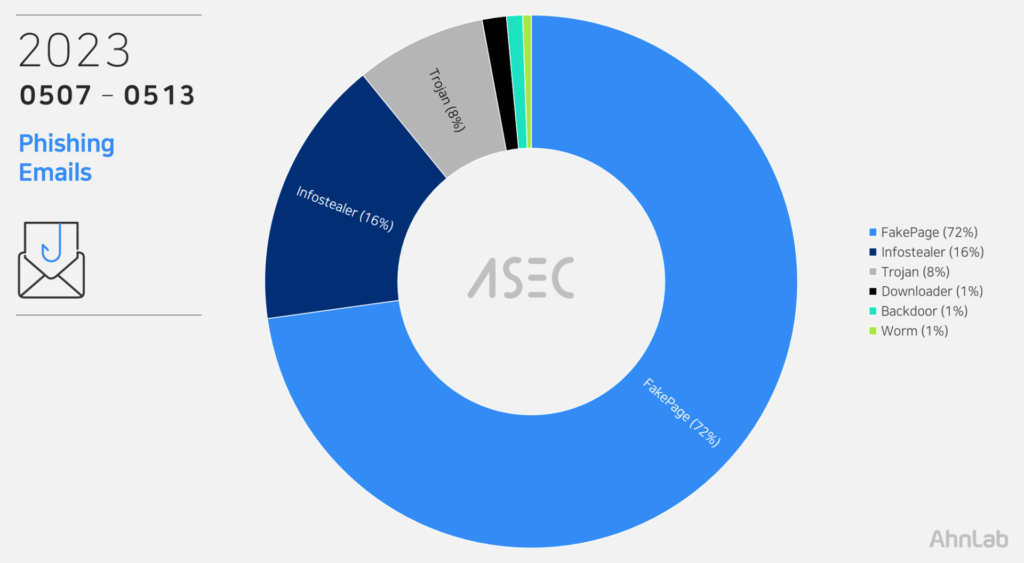
Phishing Emails
During this week, the most prevalent threat type seen in phishing email attachments was FakePage with 72%. FakePages are web pages where the threat actor has imitated the screen layout, logo, and font of the real login pages or advertising pages, leading users to enter their account and password information. The input information is sent to the threat actor’s C2 server or used to induce users to access other fake websites. See <FakePage C2> below The second in line were InfoStealers like AgentTesla and FormBook that leaks user credentials saved in web browsers, emails, and FTP clients (16%). Aside from these, Trojan (8%), Downloader (1%), Backdoor (1%), and Worm (1%) types were detected. The threat types using phishing email attachments and their order of prevalence are similar to the order of malware distribution published weekly in the <ASEC Weekly Malware Statistics>.
File Extensions in Phishing Emails
We have identified which file extensions were used by the threats above for the distribution of email attachments. FakePages were distributed with web pages scripts (HTM, HTML) that must be executed with a web browser. Other malware, including Infostealer and downloader, came attached to emails with file extensions including compressed files (RAR, Z, GZ, 7Z, etc.).
Cases of Distribution
The following are distribution cases that occurred during the week from May 7th, 2023 to May 13th, 2023. The cases will be classified into FakePage and malware types, including Infostealer, Downloader, Exploit, and Backdoor. The numbers in email subjects and attachment filenames are unique IDs and may vary depending on the email recipient. Distribution cases with Korean subjects were also found. These are cases that specifically targeted Korean users instead of propagating themselves globally using identical English subject and texts.
Case: FakePage
Email Subject
Attachment
Urgent Order Form/SW-23****019, SW-***
New Order _SW-********, SW-*********_New RFQ 0302260142BE, 0302260142BF.htm
Product Quotation Inquiry Gun_Co., Ltd****
PO_7478889393.shtml
DHL Shipment Arrival Notice [AWB#*****378004]
AWBDHLShipment55409.html
Quotation Request Sent
00155320.html
Re: Re: RE: New Order PO#41900677
JLG-SILVER contract MV AP ASTAREA.xls.htm
[FedEx] Notice on Import Tax Payment Deadline –
FedXETX81865549.htm
Confirm Document.
New-Order.2023.xls.shtml
FedEX: shared “Shipping Documents MSK1****97/110*****” with you.
Commercial Invoice._pdf.htm
FYI…. Correct the error on your records. (Invoice paid)
PAID-00241.html
[SEC=OFFICIAL:Sensitive File-ACCESS=Personal Data-Privacy-2]
Personal Data-Privacy-SecureMessageAtt.html
Re:(Scanned) Doc~Original Copy – FYI
Shipping document.html
หนังสือมอบอำนาจสำหรับข้อเสนอของคุณ
599345092876.xls.shtml
重要报价订单 (紧急处理)
Urgent#Quotation.html
Everlee Hargrove
Your.transaction.0.7495.Bitcoin.wpA2WrOTkyKUQ.pdf
Purchase Order 02823
Purchase-Order02823.htm
Protesto para: ************.******@***.com
Protesto-Consulta5512576.html
FW: confirm order
inv231pl432.shtml
RE: New Order NO.Z21239
Purchase Order NO.Z21239.pdf
REQUEST FOR QUOTATION: Invoice
REQUEST FOR QUOTATION_.html
New Ag Order
PURCHORD_802_44730_20230504082506733.html
Zariyah Gunn
Bitcoin.Transaction.0.7495.BTCeepvVzcWKiOzJMw7j2DMQaQjbwxYZ.pdf
Aliza Rich
Mining.transaction.0.7495.BTCF4arIc3oth93MmHFdcXu1.pdf
[KR]: FedEx Invoice-108321198-XXXXX3239-230414160914935
FedEx Invoice-108321198-XXXXX3239-230414160914935.shtml
Lyric Nelson
Bitcoin__Transfer__0.7495__BTCl0lysl.pdf
G AND H ENTERPRISES
doc_xls_0952023.html
Nancy Walter
Get__it__urgently__0.7495__BTCh0f8BQYsjjlMhS.pdf
RE: PO –
Dicta.pdf
Protesto para: ******.*******@***.com
Protesto-Consulta2291027.html
Please kindly see shipping invoices for payment with delivery
Payment_Receipt_11965140936.pdf.htm
Esme Clarke
Your_transaction_0.7495_Bitcoin_y9NVCAaRDijDj0TmglM1yK5PkfZn8TY4Sx.pdf
Double Charge on Credit Card – Reservation
Credit Card Statement.pdf
New Order For May P.O #3000000821
MAY P.O #3000000821 .Shtm
RIMINDER entec Confirm Your Delivery Address
AWB-Ref_#310479442.HTML
Fwd:New Order Inquiry (Davis $ Shirtliff Co,. Ltd).
Confirm_Order_inquiry.html
Payroll direct deposit receipt
Account Department.html
Case: Malware (Infostealer, Downloader, etc.)
Email Subject
Attachment
Swift Copy Euro 23,458.31
Euro Swift Copy.z
Wienerberger d.o.o. New Order
Wienerberger_d.o.o_23052291.img
FW: WIRE INSTRUCTIONS P384757
Wire Instruction P85793.7z
RE: Surat Pesanan – RFQ
PT0012305.PDF.rar
FW: Bulk Units
VB-SM1248.docx
PURCHASE ORDER ( 231062 )
PO-231062.zip
Inquiry
ESU51092W310.ISO
RE: [EXTERNAL] RE: Confirmación del pedido
Se adjunta factura proforma.zip
[FGIP2 Project / ***] Request for Quotation MR-001 FGIP2 PJT Package / ****
[FGIP2 Project ***] Request for Quotation MR-001 FGIP2 PJT Package ****.rar
1*40GP_ ECU Urgent RFQ
QS20202310109051_ErgunMakina Ind_40GP_50CBM.xz
Price
DES310941H5.ISO
SWIFT Payment Receipt For Invoice
SWIFT Payment Receipt For Invoice.rar
Re: CNS-1093220
CNS310932F20.IMG
RE:BSM011523Y
BSM011523Y.ISO
[SPAM] RE: DEBIT NOTE
DEBIT NOTE.rar
50% ADVANCE CUSTOMER PAMENT TO ******.****
TT copy -company invoice for clien #090523.r01
cool pictures
privateact.exe
E-Ekstre Servisi
Ekstre.LZH
Fatura Bilgilendirme
Fatura.gz
New Order
43000690531TEZ_S order.z
Para Transferi
TRANSFERI.UUE
PDA Remittance Receipt
PDA Remittance Receipt.rar
PO_29335_MOBRAY_CLASS_150_PROJECT_CB
PO_29335_MOBRAY_CLASS_150_PROJECT_CB.r01
price list
44XYZ_S Quote.z
Proforma Invoice/ USD bank details
******** Chase.rar
Quotation
quote.gz
RE: Amended Purchase Order
AMENDED PURCHASE ORDER.rar
Re: orden de compra
orden de compra.gz
RE: quote request
55FZ_S Quote.z
Release Order No for BL MEDUAF820164
Bill of Lading and Letter of Authority# 023.rar
RFQ _#CIF/ FOR Hyderabad
RFQ _#CIF FOR Hyderabad.r01
RFQ$$FOB_BASESRep. of KOREA
RFQ$$FOB_BASESRep. of KOREA.r00
The ASEC analysis team has selected keywords that users must look out for, based on the distribution cases above. If these keywords are included in the subject of the email, or if the same characteristics are found, users must exercise strict caution as they may be phishing emails from threat actors.
Keyword to Beware of: ‘Quotation’
The keyword for this week is ‘Quotation’. The threat actor impersonated Korean companies and distributed phishing emails (Quotation Request Sent, Product Quotation Inquiry) requesting for quotations. The body of the phishing emails were disguised to look like that of actually used emails. It seems that the threat actor obtained this through the affected company or leaked email accounts. A web page script (00155320.html, PO_78912290586868.shtml) file is attached to the email. This HTML file is a fake page disguised as the company’s page and a Microsoft Excel, and the information entered by the user is sent to the operator’s server. A web page script (00155320.html, Po_78912290586868.shtml) is being distributed by emails disguised like below and the information inputted by users are sent to the following threat actor servers:
Threat Actor URL (Quotation Request Sent): https[:]//bilalid[.]tk/fgh/na1[.]php
Threat Actor URL (Product Quotation Inquiry): https[:]//checkengineer[.]com/er/auth[.]php
FakePage C2 URL
When users enter their IDs and passwords on the login pages among the FakePages created by the threat actor, their information is sent to the attacker’s server. The list below shows the threat actor’s C2 addresses of fake login pages distributed during the week.
https[:]//formspree[.]io/f/xdovnyrz
http[:]//liagestoraimobiliaria[.]com[.]br/wp-content/zzzzzZZZ/fdx[.]php
https[:]//www[.]krabiview[.]com/wp-content/themes/twentythirteen/line/exee[.]php
https[:]//www[.]sandandstoneconstruction[.]com/wp-includes/fddx/dhlrr[.]php
https[:]//woodless-neutron[.]000webhostapp[.]com/[.]cmd/error/encodede[.]php
http[:]//baltik-memorial[.]ru/wp-includes/Ex/Excel[.]php
https[:]//cianindustries[.]com/view/pop/xlss[.]php
https[:]//dkglobaljobs[.]com/static/js/will/exee[.]php
https[:]//submit-form[.]com/YxyXVvWR
https[:]//formspree[.]io/f/xwkjrjbp
https[:]//californiaapostillenotary[.]com/wp-admin/PY/cloudlog[.]php
https[:]//cozuretabi[.]com/wp-includes/widgets/juuusssst/justgm[.]php
https[:]//opalcoms[.]nz/win/auth[.]php
https[:]//submit-form[.]com/4X38L2pE
https[:]//submit-form[.]com/UwzTXAQr
https[:]//heraldic-governors[.]000webhostapp[.]com/dhlc[.]php
https[:]//checkengineer[.]com/bran/auth[.]php
Attacks using phishing emails are disguised with content that can easily deceive users, such as invoices and tax payments, to induce users to access fake login pages or execute malware. Fake login pages are evolving by the second to closely resemble the original pages. The attackers pack malware in compressed file formats to escape the attachment scans of users’ security products. Users must practice strict caution and refer to recent cases of distribution to avoid being exposed to infection by malicious phishing emails. The ASEC analysis team recommends users follow the email security guidelines below.
Do not execute links and attachments in emails from unverified senders until they are proven to be credible.
Do not enter sensitive information such as login account credentials until the site is found to be reliable.
Do not execute attachments with unfamiliar file extensions until they are found to be reliable.
Use security products such as antimalware software.
According to the MITRE ATT&CK framework, phishing email attacks correspond to the following techniques.
Phishing for Information (Reconnaissance, ID: T1598[1])
Phishing (Initial Access, ID: TI1566[2])
Internal Spearphishing (Lateral Movement, ID: T1534[3])
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.
The post ASEC Weekly Phishing Email Threat Trends (May 7th, 2023 – May 13th, 2023) appeared first on ASEC BLOG.
Article Link: https://asec.ahnlab.com/en/53103/
1 post – 1 participant

