ASEC Weekly Phishing Email Threat Trends (May 21st, 2023 – May 27th, 2023)
AhnLab Security Emergency response Center (ASEC) monitors phishing email threats with the ASEC automatic sample analysis system (RAPIT) and honeypot. This post will cover the cases of distribution of phishing emails during the week from May 21st, 2023 to May 27th, 2023 and provide statistical information on each type. Generally, phishing is cited as an attack that leaks users’ login account credentials by disguising as or impersonating an institute, company, or individual through social engineering methods. On a broader note, the act is a technical subterfuge that enables the threat actor to perform attacks such as information leaks, malware distribution, and fraud against various targets. The focus of this post will be on the fact that phishing attacks mainly occur through emails. We will also provide a detailed classification of various attack methods that are based on phishing emails. Furthermore, we will make an effort to minimize user damage by introducing new attack types that have never been found before and emails that require users’ caution, along with their keywords. The phishing emails covered in this post will only be those that have attachments. Emails that have malicious links in the body without attachments will be excluded.
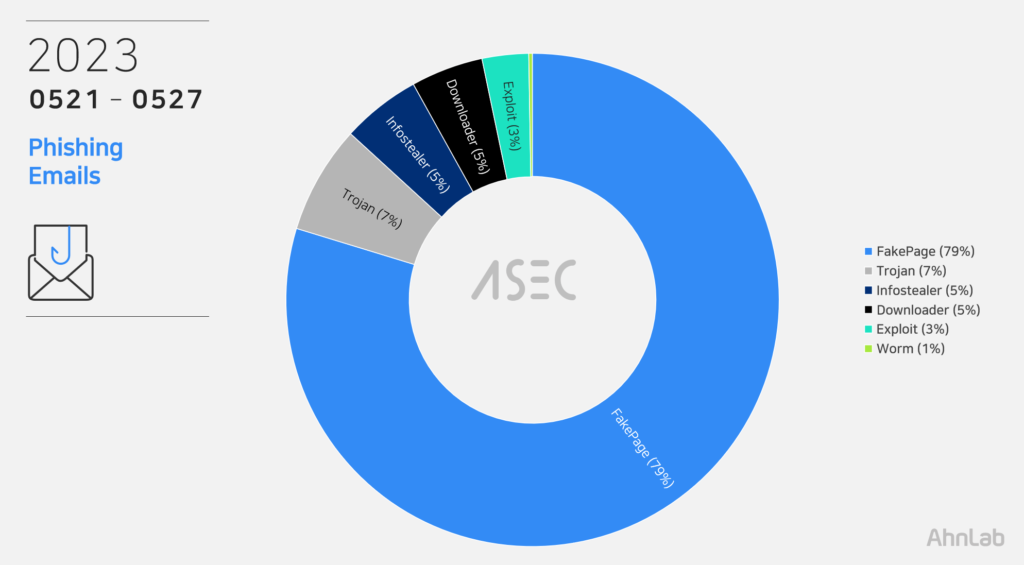
Phishing Emails
During this week, the most prevalent threat type seen in phishing email attachments was FakePage with 79%. FakePages are web pages where the threat actor has imitated the screen layout, logo, and font of the real login pages or advertising pages, leading users to enter their account and password information. The input information is sent to the threat actor’s C2 server or used to induce users to access other fake websites. See <FakePage C2> below. The second most collected type was Trojan, which took up 15%. It was then followed by Infostealers (5%) like AgentTesla and Formbook that leaks user credentials saved in web browsers, emails, and FTP clients, then by Downloader (5%), Exploit (3%), and Worm (1%). The threat types using phishing email attachments and their order of prevalence are similar to the order of malware distribution published weekly in the <ASEC Weekly Malware Statistics>.
File Extensions in Phishing Emails
We have identified which file extensions were used by the threats above for the distribution of email attachments. FakePages were distributed through web pages script (HTM, HTML, SHTML) documents that must be executed with a web browser. Other malware, including Infostealer and downloader, came attached to emails with file extensions including compressed files (RAR, Z, GZ, 7Z, etc.).
Cases of Distribution
The following are distribution cases that occurred during the week from May 21st, 2023 to May 27th, 2023. The cases will be classified into FakePage and malware types, including Infostealer, Downloader, Exploit, and Backdoor. The numbers in email subjects and attachment filenames are unique IDs and may vary depending on the email recipient. Distribution cases with Korean subjects were also found. These are cases that specifically targeted Korean users instead of propagating themselves globally using identical English subject and texts.
Case: FakePage
Email Subject
Attachment
Account Password Warning
Verify.shtml
[FedEx®] Delivery Notice – Document Arrival Notice?
Shipping Document_Bill of Lading.Pdf.htm
Re:(Scanned) Doc~Original Copy – FYI
Original Shipping document BL, PL, CI_.htm
Re: Purchase Order-#3687364
PO_#3687364.shtml
[FedEx] Customs Payment Guide (Tax Invoice)
AWB4698559.html
Quote Request For New Project LLC
AIS_Purchase Agrmt_pdf.htm
Re: Fwd: URGENT: PROOF OF PAYMENT
PROOF OF PAYMENT.html
FW:ATTACHED SWIFT COPY 5/18/2023 11:19:22 p.m
Payment copy.html
DHL Shipment Document Arrival [AWB#*****378434]
ShippingDocumentDHL.html
CIPC Annual Returns-K2023739309 Tracking reference: 9382857991
COR15.1A.html
Come on, quickly withdraw your +16817$! The account is not blocked yet
Your_accounts_with_a_balance_of_22988%24_will_be_blocked-1103.pdf
SWIFT COPY RECEIPT
PaymentSwiftCopy.html
Regarding payment for Po No. : 4500250395
ParcelArrivalShipment.html
Re: Congratulations You Have WON !!!
Official Reward Payment Notification.pdf
Re: Re:Wire confirmation copy
Wire Confirmation copy.pdf
DHL Cargo arrival information [AWB#*****378761]
invoice.html
Monthly statement 23/05/23
Statement0523.html
Re: Purchase Order
Quote.html
Please see the attached document for our paid inv # 10047
Remittance_Statement_90493.htm.
Email delivery activity log.
Email delivery activity log.shtml
❶ Mailbox Quota almost Full.
entec more storage.html
电子发票通知
SF_INV.html
New Quotation Request PO# 220979150/Contract
PO# 220979150_Contract.HTM
DHL Shipment Notification – Shipping Document – Shipment Tracking
Original Shipping Doc#393929.pdf.htm
Re: Fwd: brass wire(payment advice)
Payment advice.html
Unpaid invoices
INVOICE .SHTML
Invoice for review from *******@*****e*c.kr
samilenc_invoice3271.html
Find Attached For Your Urgent Attention
P1008357421.html
Case: Malware (Infostealer, Downloader, etc.)
Email Subject
Attachment
[DHL] Acceptance of Import Declaration (Payment Before Acceptance) – 787988793436
DHL TAX INVOICE..rar
RECEIPT FOR INVOICE MC20230414A (22MAY2023)
RECEIPT FOR INVOICE.rar
Request for Quotation 94573-LAR&SAF CAPSA/BIO OILS
RFQ-945730101-B0000005023019.cab
Shipment Delivery Address *(Required) contact form
Required contact form..rar
RE: RE: FW: 2023/7/24 order shipment
New24 order shipment.docx
İş Bankası-19.05.2023 08:00-22.05.2023 07:
53060033570_20230522_08055750_HesapOzeti.pdf.lzh
VESSEL : DANICA // PISTON RING + GASKET
DANICA PISTON RING + GASKET.rar
ORDER INQUIRY
SKMB67091253Y.ISO
RE: REMT 049835 SWIFT MT103
MT103 REF USD .7z
FW: Purchase Order Shipped
HOBL_WEB230130599.7z
Inquiry for new order
scan.zip
Please review your July 2022 offer
PLAYGROUND PROJECT – 2022089928 – KDF.7z
Re: Confirmación pedido de compra
nuevo pedido 008794897.xlsx.img
Confirming – de pago.
008s06523610054680b6011375030062022.rar
RE: Faktur Mei 2023.
PT230522.PDF.rar
payment confirmation copy
$153,430.00.pdf.rar
RE: Νέα παραγγελία
0324352432563.zip
CV Debora Lopez
Curriculum Vitae Debora lopez.zip
Complain Case: Issues Of Damaged Goods
Pictures Of Damaged Goods__________________pif.Z
DHL Shipment Notification
DHL AWB #5401214457 – 20230526.gz
Fw: PAYMENT COPY
20230524.012563647892033.TRF.gz
New Order PO-371/2020
PO-37101020-PDF.rar
PASSWORD EXPIRED
Quotation##2005023.r01
PO-000001306
PO-000001306.z
Purchases Order // PO23100080
PO23100080-pdf.gz
Purchases Order // PO971100044
PO971100044.gz
RE; Advice from Standard Chartered Bank
MT103.xls
RE: CONTRACT FOR SUPPLY CONFIRMATION // PO#332022-23
SUPPLY CONTRACT for PO#332022-23.pdf.z
RE: New Shipment Order / Urgent Request Approval of Draft Shipping Docs (BL/SZOE23050007)
SHIPPING DOCS.xls
RE: NEW SHIPMENT UPDATE // 1688 // ISF DETAILS
BL 1688.pdf.z
RE: order
QU10001005597.z
Re: Petrofac Payment Swift For Overdue Invoices
Payment Swift-pdf.gz
Re: URGENT: New Orders (PO#1164031)
PO#1164031.r17
Re[2]: super nice photos don’t show
priv-phot.jpg.scr
RE:Purchase Order No. I20220052
Order No. I20220052.xls
Your latest DHL invoice : KHIR001231448 for ******.shop
KHIR001231448.pdf.z
The ASEC analysis team has selected keywords that users must look out for, based on the distribution cases above. If these keywords are included in the subject of the email, or if the same characteristics are found, users must exercise strict caution as they may be phishing emails from threat actors.
Keywords to Beware of: ‘Zimbra’
The keyword for this week is ‘Zimbra’ whose login page is used as a disguise for phishing emails. Zimbra is collaborative software with an email server and web client. The threat actor abused Zimbra’s login page to distribute phishing emails and steal the targets’ account credentials. The phishing email discovered recently is designed so that when the user clicks the “Keep My Password” button they are redirected to a phishing site disguised as the Zimbra login page. As such, when entering personal information such as ID and password on a web page, users must check if the address of the page that requires such information is trustworthy.
Phishing URL: https[:]//walkingmapsqld[.]com/.home/edit/battle/form.php
FakePage C2 URL
When users enter their IDs and passwords on the login pages among the FakePages created by the threat actor, their information is sent to the attacker’s server. The list below shows the threat actor’s C2 addresses of fake login pages distributed during the week.
http[:]//liagestoraimobiliaria[.]com[.]br/wp-content/ex/exee[.]php
https[:]//www[.]spgiutar[.]com/fe/fdpxoGur23f[.]php
https[:]//submit-form[.]com/M9g3KLqI
https[:]//formspree[.]io/f/xrgvdwqd
https[:]//lightup-solar[.]com/gods/dhll%20(1)[.]php
https[:]//sercex[.]com/justgm[.]php
https[:]//submit-form[.]com/XpImoBBB
https[:]//agrotehnika-mp[.]ru/@T/Daemon[.]php
https[:]//submit-form[.]com/GOXYSUaX
https[:]//alliedbmcltd[.]co[.]uk/hiw[.]php
https[:]//walkingmapsqld[.]com/[.]home/edit/battle/form[.]php
Attacks using phishing emails are disguised with content that can easily deceive users, such as invoices and tax payments, to induce users to access fake login pages or execute malware. Fake login pages are evolving by the second to closely resemble the original pages. The attackers pack malware in compressed file formats to escape the attachment scans of users’ security products. Users must practice strict caution and refer to recent cases of distribution to avoid being exposed to infection by malicious phishing emails. The ASEC analysis team recommends users follow the email security guidelines below.
Do not execute links and attachments in emails from unverified senders until they are proven to be credible.
Do not enter sensitive information such as login account credentials until the site is found to be reliable.
Do not execute attachments with unfamiliar file extensions until they are found to be reliable.
Use security products such as antimalware software.
According to the MITRE ATT&CK framework, phishing email attacks correspond to the following techniques.
Phishing for Information (Reconnaissance, ID: T1598[1])
Phishing (Initial Access, ID: TI1566[2])
Internal Spearphishing (Lateral Movement, ID: T1534[3])
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.
The post ASEC Weekly Phishing Email Threat Trends (May 21st, 2023 – May 27th, 2023) appeared first on ASEC BLOG.
Article Link: ASEC Weekly Phishing Email Threat Trends (May 21st, 2023 – May 27th, 2023) – ASEC BLOG
1 post – 1 participant


