116 Ransomware Files Infecting Linux and Windows Systems Were Discovered on the PyPI Repository
116 Ransomware Files Infecting Linux and Windows Systems Were Discovered on the PyPI Repository.
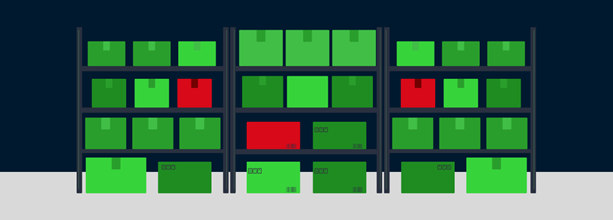
A group of cybersecurity experts has discovered a collection of 116 harmful software packages on the Python Package Index (PyPI) repository. These packages are specifically created to infiltrate Windows and Linux operating systems with a unique type of hidden access point.
“In certain instances, the ultimate payload consists of a modified version of the notorious W4SP Stealer, or a basic clipboard monitor designed to illicitly acquire cryptocurrency, or both,” stated ESET researchers Marc-Etienne M. Léveillé and Rene Holt in a study released earlier this week.
The packages have garnered an approximate total of 10,000 downloads since May 2023.
The perpetrators responsible for the activity have been detected employing three methods to combine harmful code into Python packages. These methods include utilizing a test.py script, inserting PowerShell within the setup.py file, and incorporating it in a concealed manner within the __init__.py file.
Regardless of the approach employed, the ultimate objective of the campaign is to infiltrate the intended host with malicious software, specifically a backdoor that can execute commands remotely, extract data, and capture screenshots. The backdoor module is coded in Python for Windows and in Go for Linux.
Alternatively, the attack sequences also conclude with the implementation of W4SP Stealer or a clipper malware intended to closely monitor a victim’s clipboard activity and replace the original wallet address, if it exists, with an address controlled by the attacker.
This discovery represents the most recent occurrence in a series of corrupted Python packages that attackers have deliberately released to contaminate the open-source ecosystem and disseminate a variety of malicious software for supply chain attacks.
Furthermore, it is the most recent inclusion in a consistent flow of fraudulent PyPI packages that have served as a covert conduit for disseminating stealer malware. In May 2023, ESET disclosed the discovery of a group of libraries designed to spread Sordeal Stealer, a malware that incorporates functionalities from W4SP Stealer.
In the previous month, deceptive packages posing as harmless obfuscation tools were discovered to distribute a malicious software known as BlazeStealer, which is designed to steal sensitive information.
The researchers emphasized that Python writers should meticulously examine the code they obtain, particularly by scrutinizing these techniques, before putting it on their systems.
The disclosure is a result of the identification ofnpm packages that were specifically designed to target an undisclosed financial institution as part of a highly sophisticated exercise to simulate attacks from advanced adversaries. The names of the modules, which included an encrypted blob, have been suppressed for the purpose of preserving the anonymity of the organization.
“According to software supply chain security firm Phylum, the decrypted payload includes a cleverly embedded binary that stealthily sends user credentials to an internal Microsoft Teams webhook within the target company,” was revealed by Phylum last week.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
The post 116 Ransomware Files Infecting Linux and Windows Systems Were Discovered on the PyPI Repository appeared first on .


